|
I
used original french disks IPF
#1736 (4 disks)
- Action Replay or HRTMon, DevPac (or AsmOne)
- resourcer/debugger (AR, Mega-Mon...)
(see ToolDisks)
|
|
It's
a dos game : no disk based protection. Start the
game...it's a password protection |
not
really easy, because of many ways to find keyboard routines.
If you stop the game with AR and disassemble, you reach
each time graphics routine...
but we have the location of the program in memory. (with
512K slow fast, the program is at $C0xxxx. address could
change).
AR
break :
We can see on the screen the text "protection".
perhaps we could find the text in memory ? or the code
is 6 chars long. Why not searching a cmpi.b #6 ($c390006)
(or cmpi.w #6, cmp.b...)
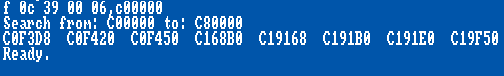
f 0c 39 00 06,c00000 ; CMPI.B #6
Good
results; combined with the search of letters, we can see
"P" "R" "O"... near the
"cmp".
n c0f300
Each address test the same variable at C19252. In this
case there are 2 test routines : one near C0F3D8 and another
near C19168. (I skipped the C168B0 because it's not the
same address tested)
Here
is the routine 1:
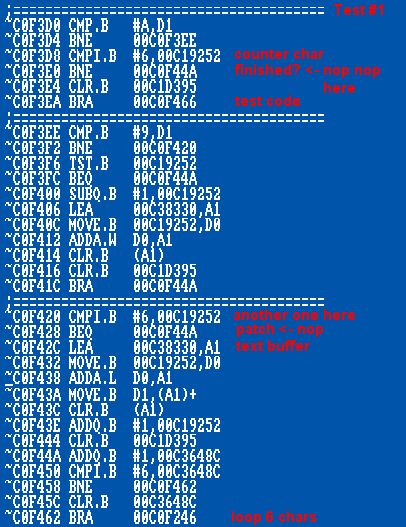
Exit
AR and type some letters.
break, take a look at C38330 : here is the chars. we have
found the routine!
it's a loop for testing the 6 chars.
at C0F3EA it's the end, go to test code (C0F466).
We can break the loop of 6 chars : put 2 NOP (4e71 4e71)
at C0F3E0.
Another cmpi.b #6 exists at C0F420 : 2x nop at C0F428.
Exit AR, press Return. That doesn't work.
Need
to patch the second routine.
Second test routine:
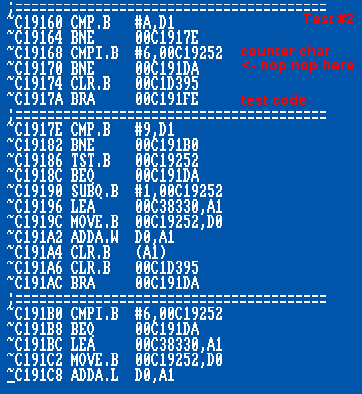
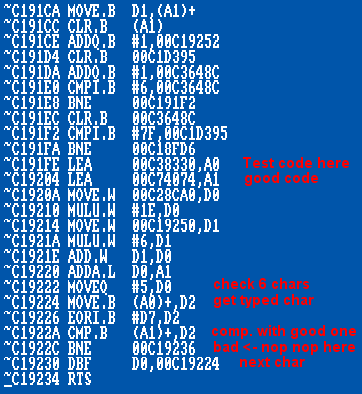
at
C19170, put 2 Nop.
That
works. But the code is still checked.
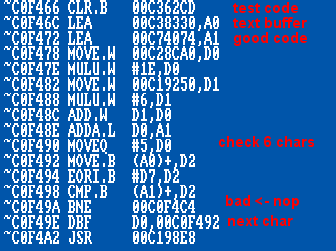
The
2 testcode routs are at C0F466 and C191FE.
NOP the cmp result at lines C0F49A and C1922C. loop
6 chars but never check them ;)
this
second test at C191FE is the second password test near
the end of the game.
Exit
AR, press Return. OK!

At the protection screen, press Return without having
to type 6 chars.
Now
let's go with disassembler for having the whole program
and patch it.
Definitive
patch is done on the fly with a small code like "endrun"
using LoadSeg()
a "quick" way for testing : patch directly
the executable file "flashback with hexa editor
or load file "flashback" as binary (original
no compressed version - 186 kb).
SKIP THE PROTECTION SCREEN
the first protection start at offset D694 and is called
once (8B8)
put a $4E75 (RTS) at D694
(German Version : D8FA - called at 8B8)
the second protection start at offset 38AC and is called
twice (463A,4782)
put a $4e75 (RTS) at 38AC
(German Version : 3A40 - seems not used)
IF YOU WANT TO SHOW THE PROTECTION SCREEN
search for cmp/protection, find routines, and change
bytes.
binary offsets are (+$30 skip header) (from French version)
:
put $4e714e71 (NOP NOP) at :
- D940 (D970) first protection (called at start)
- D9FC (DA2C) (ger.: DC28)
- 3BB0 (3BE0) second protection (called twice)
- 3BF8 (3C28)
- 3C6A (3C9A) second password test near the end
German
version : second protection not used
but the program compare the last line of the first protection
at offset 236A4 :
cmpi.l
#$66000008,DC28"
beq xxxx ; ok
... |
The
best way is to use skip all the protection with RTS
at D8FA
else offsets to patch with NOP are :
- DB6C, DC28
but replace the BEQ at 236AE by a (wonder) BRA = $60
$66000008 = it's the "bne xxxx" we have nopped
in the test code 2 !
How
to verify if an other protection is hidden somewhere?
play the whole game ;)
you can use already known levels codes :
(french version)
mode Easy: back, loop, cine, good, spiz, bios, hall
mode normal : play, toit, zapp, linx, scsi, gary, pont
mode hard : clop, cara, cale, font, hash, fibo, tips
(english version)
mode Easy: wind, spin, kava, hiro, test, gold, wall
mode normal: fire, burn, eggs, gurt, chip, tree, bold
mode hard : mine, your, nest, line, lisa, mary, mice
Or
search if the program check itself if he was modified
(hmm...this kind of check should be done each time)
:
search the lines nopped if they are tested somewhere
:
C0F3E0 (off 3BE0), C0F49A (off 3C9A), C19170 (off D970),
C1922C (off DA2C)
no
results in French versions.
some others versions exist: no more in English version.
Test
the full game. It seems ok now.
Quick
crack with AR Video on Youtube
Update 28 feb. 2017 : Missing
Dialog Bug on all Amiga versions
during the cinematic in level 5.
2008
(c) Heavy
Download
: (upd. include the Level 5 Missing Dialog
Bug Patch by StingRay and Pants)
- Patch crack
(replace "endrun flashback" in startup-sequence)
- Cracked disk
- Cracked executable
(alt. way)
|







